Reverse Engineering is Not Hard with LLM Powered Tools
by Reflare Research Team on Apr 9, 2024 7:07:53 AM
With the advent of LLM-powered tools, the intricate task of reverse engineering compiled software is becoming more manageable, allowing newcomers and seasoned professionals to navigate the process more easily. First Published 9th April 2024 The reversing engineer. 4 min read | Reflare …
Understanding the Post-Exploitation Jargon and Concepts
by Reflare Research Team on Feb 29, 2024 11:43:52 AM
Post-exploitation is the art of the 'what next?' for cyber attackers, a critical phase where they leverage access to dig deeper, escalate privileges, and extract valuable data. First Published 29th February 2023 Post exploitation. 4 min read | Reflare Research Team Imagine yourself as …
Is Your CPU Leaking Sensitive Data?
by Reflare Research Team on Jan 2, 2024 1:20:36 PM
In a recent turn of events, Intel and AMD are once again under the cybersecurity spotlight, with critical vulnerabilities found in their CPUs, challenging the notion of hardware-level security in modern computing.
Exploring Data Science and Machine Learning the Cybersecurity Way
by Reflare Research Team on Dec 12, 2023 3:23:16 PM
Focusing on the dynamic interplay between artificial intelligence and cybersecurity, we cast an eye over some of the more valuable projects in the areas of malware detection and software vulnerability analysis.
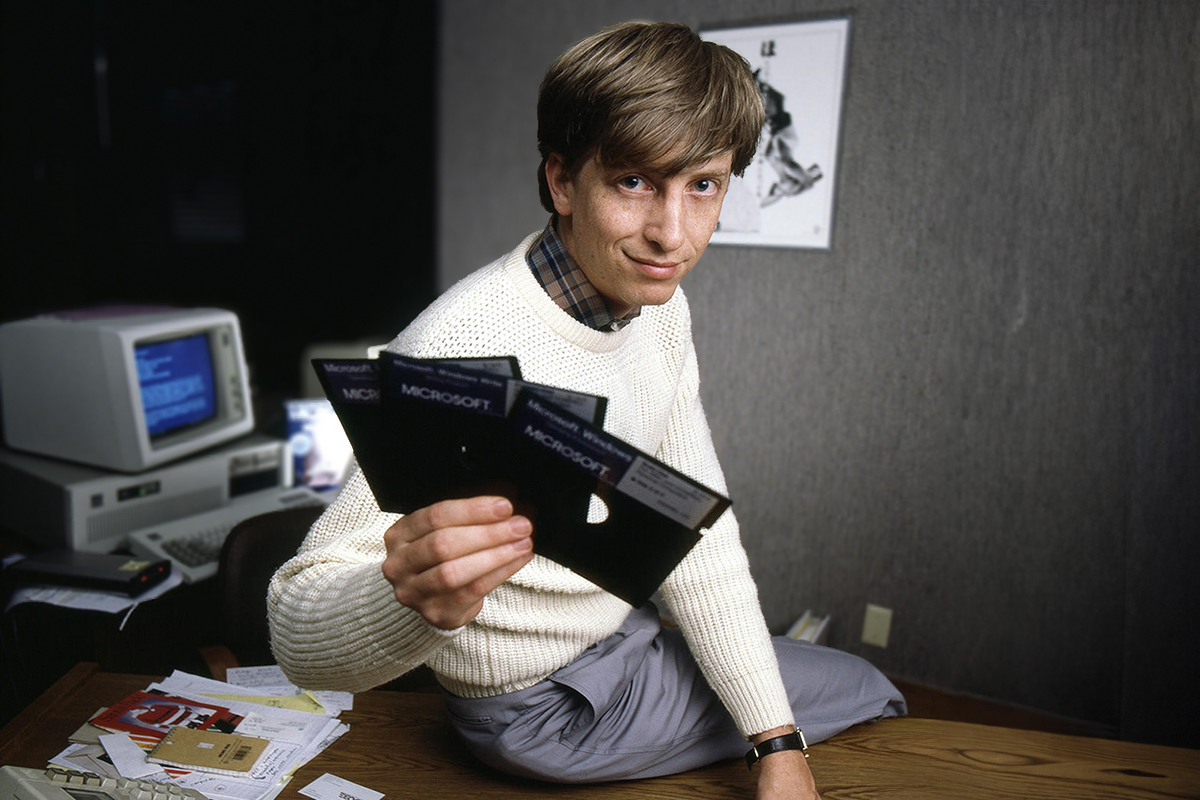
The Benefits of Studying Classic Systems and Exploitation Techniques
by Reflare Research Team on Nov 3, 2023 8:08:00 PM
In a rapidly evolving technological world where it's easy to be dazzled by the cutting-edge, the wisdom and treasure to be found in the exploitation techniques of yesteryear remains timeless.
FTX Hacker Finally Making a Move
by Reflare Research Team on Oct 5, 2023 8:06:00 PM
After FTX's monumental crash and a hacker's theft of hundreds of millions, the crypto world searched for answers, and just when the trail seemed cold, unexpected activity sparked from the suspected hacker's wallet.
Hacking Large Language Models
by Reflare Research Team on Sep 2, 2023 8:04:00 PM
Top AI companies have challenged hackers to trick chatbots into producing inappropriate or inaccurate answers. We explore the inner workings of Large Language Models (LLMs), the innovative techniques to exploit them, and the critical safeguards necessary to ensure their secure and eth …
It's Time for Corporate Leaders to Prioritise Cybersecurity Over Comfort and Convenience
by Reflare Research Team on Aug 1, 2023 8:02:00 PM
A recent breach in Nagoya has revealed (again) the illusion that maintaining outdated software is more cost-effective than upgrading to secure systems, particularly in organisations predominantly run by leaders who are comfortable with older technologies.
The MOVEit Hack: What You Need to Know
by Reflare Research Team on Jul 4, 2023 8:01:00 PM
The intricacy of the MOVEit hack is having a profound impact on many public and private organisations. But will these organisations learn the crucial cybersecurity lessons this moment will ultimately teach them?
How to Set Meaningful Cyber Security Development Goals
by Reflare Research Team on Jun 27, 2023 6:59:00 PM
Having an acute understanding of not just the 'what', but the 'why' your staff members require specific capability development is critical for deploying training that gives the business what it really needs.